Ten years ago, a major cyberattack was discovered on the Australian company NewSat.
The hashtag#network had to be rebuilt from scratch in secret. That work took almost a year and cost nearly $1 million.
One former tech employee at the company told the press it was understood by the staff that NewSat had sensitives communications interception equipments in its data centre (including highly confidential plans for a privately financed geostationary communications satellite). Because of the company’s state of information hashtag#security, the Australian Government had refused to hand NewSat a restricted NSA hashtag#encryption tool for its satellites.
Intelligence services have stated that in these cases, they suspect the attackers were sponsored by China.
“Given we were up against China, state-sponsored, a lot of money behind them and a lot of resources and we were only a very small IT team, it certainly wasn’t a fair fight for us”, said Newsat’s former IT manager Daryl Peter.
While the company has carried communications for resources and fossil fuel companies, as well as the US military’s campaign in Afghanistan, Mr Peter said the real target for the cyber infiltration was its plans for a Lockheed Martin-designed hashtag#satellite dubbed Jabiru-1.
“The way it was described to us was they are so deep inside our network it’s like we had someone sitting over our shoulder for anything we did” said Daryl Peter.
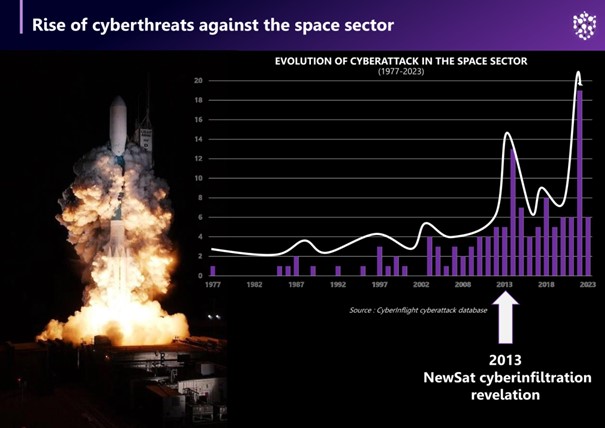
Cybersecurity issues in the hashtag#space sector have taken a new turn recently, but they are not new. This attack demonstrates that hashtag#cyber espionage activities against space infrastructures have been used intensively since the early 2010s.
The number of cyberattacks targeting the space sector every year continues to rise. CyberInflight collects and analyzes these attacks as well as threat actors and cybersecurity organizations involved in the space sector. This research and information analysis can be found in our market intelligence report on space cybersecurity.
For further information about our report or our set of databases, please contact us at the following address: research@cyberinflight.com